The Slow-Motion Collapse of the American Empire
By William J. Astore
Source: TomDispatch.com
Jump into your time machine and let me transport you back to another age.
It’s May 2001 and the Atlantic Monthly has just arrived in the mail. I’m tantalized by the cover article. “Russia is finished,” the magazine announces. The subtitle minces no words: “The unstoppable descent into social catastrophe and strategic irrelevance.” Could it be that the country I had worried most about as a military officer during all those grim years of the Cold War, the famed “Evil Empire” that had threatened us with annihilation, was truly kaput, even in its Russian rather than Soviet guise?
Sixteen years later, the article’s message seems just a tad premature. Today’s Russia surely has its problems — from poverty to pollution to prostitution to a rickety petro-economy — but on the geopolitical world stage it is “finished” no longer. Vladimir Putin’s Russia has recently been enjoying heightened influence, largely at the expense of a divided and disputatious superpower that now itself seems to be on an “unstoppable descent.”
Sixteen years after Russia was declared irrelevant, a catastrophe, finito, it is once again a colossus — at least on the American political scene, if nowhere else. And that should disturb you far less than this: more than a generation after defeating the Soviet Union in the Cold War, the United States of 2017 seems to be doing its level best to emulate some of the worst aspects of its former foe and once rival superpower.
Yes, the U.S. has a Soviet problem, and I’m not referring to the allegations of the moment in Washington: that the Trump campaign and Russian officials colluded, that money may have flowed into that campaign via Russian oligarchs tied to Putin, that the Russians hacked the U.S. election to aid Donald Trump, that those close to the president-elect dreamed of setting up a secret back channel to Moscow and suggested to the Russian ambassador that it be done through the Russian embassy, or even that Putin has a genuine hold of some sort on Donald Trump. All of this is, of course, generating attention galore, as well as outrage, in the mainstream media and among the chattering classes, leading some to talk of a new “red scare” in America. All of it is also being investigated, whether by congressional intelligence committees or by former FBI director — now special counsel — Robert Mueller.
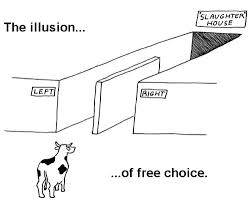
When it comes to what I’m talking about, though, you don’t need a committee or a counsel or a back channel or a leaker from some intelligence agency to ferret it out. Whatever Trump campaign officials, Russian oligarchs, or Vladimir Putin himself did or didn’t do, America’s Soviet problem is all around us: a creeping (and creepy) version of authoritarianism that anyone who lived through the Cold War years should recognize. It involves an erosion of democratic values; the ever-expanding powers exercised by a national security state operating as a shadow government and defined by militarism, surveillance, secrecy, prisons, and other structures of dominance and control; ever-widening gaps between the richest few and the impoverished many; and, of course, ever more weapons, along with ever more wars.
That’s a real red scare, America, and it’s right here in the homeland.
In February, if you remember — and given the deluge of news, half news, rumor, and innuendo, who can remember anything these days? — Donald Trump memorably compared the U.S. to Russia. When Bill O’Reilly called Vladimir Putin “a killer” in an interview with the new president, he responded that there was little difference between us and them, for — as he put it — we had our killers, too, and weren’t exactly innocents abroad when it came to world affairs. (“There are a lot of killers. You think our country’s so innocent?”) The president has said a lot of outlandish things in his first months in office, but here he was on to something.
My Secret Briefing on the Soviet Union
When I was a young lieutenant in the Air Force, in 1986 if memory serves, I attended a secret briefing on the Soviet Union. Ronald Reagan was president, and we had no clue that we were living through the waning years of the Cold War. Back then, believing that I should know my enemy, I was reading a lot about the Soviets in “open sources”; you know, books, magazines, and newspapers. The “secret” briefing I attended revealed little that was new to me. (Classified information is often overhyped.) I certainly heard no audacious predictions of a Soviet collapse in five years (though the Soviet Union would indeed implode in 1991). Like nearly everyone at the time, the briefers assumed the USSR would be our archenemy for decades to come and it went without saying that the Berlin Wall was a permanent fixture in a divided Europe, a forever symbol of ruthless Communist oppression.
Little did we know that, three years later, the Soviet military would stand aside as East Germans tore down that wall. And who then would have believed that a man might be elected president of the United States a generation later on the promise of building a “big, fat, beautiful wall” on our shared border with Mexico?
I wasn’t allowed to take notes during that briefing, but I remember the impression I was left with: that the USSR was deeply authoritarian, a grim surveillance state with an economy dependent on global weapons sales; that it was intent on nuclear domination; that it was imperialist and expansionist; that it persecuted its critics and dissidents; and that it had serious internal problems carefully suppressed in the cause of world mastery, including rampant alcohol and drug abuse, bad health care and declining longevity (notably for men), a poisoned environment, and an extensive prison system featuring gulags. All of this was exacerbated by festering sores overseas, especially a costly and stalemated war in Afghanistan and client-states that absorbed its resources (think: Cuba) while offering little in return.
This list of Soviet problems, vintage 1986, should have a familiar ring to it, since it sounds uncannily like a description of what’s wrong with the United States today.
In case you think that’s an over-the-top statement, let’s take that list from the briefing — eight points in all — one item at a time.
1. An authoritarian, surveillance state: The last time the U.S. Congress formally declared war was in 1941. Since then, American presidents have embarked on foreign wars and interventions ever more often with ever less oversight from Congress. Power continues to grow and coalesce in the executive branch, strengthening an imperial presidency enhanced by staggering technologies of surveillance, greatly expanded in the aftermath of the 9/11 terrorist attacks. Indeed, America now has 17 intelligence agencies with a combined yearly budget of $80 billion. Unsurprisingly, Americans are surveilled more than ever, allegedly for our safety even if such a system breeds meekness and stifles dissent.
2. An economy dependent on global weapons sales: The U.S. continues to dominate the global arms trade in a striking fashion. It was no mistake that a centerpiece of President Trump’s recent trip was a $110 billion arms deal with Saudi Arabia. On the same trip, he told the Emir of Qatar that he was in the Middle East to facilitate “the purchase of lots of beautiful military equipment.” Now more than ever, beautiful weaponry made in the U.S.A. is a significant driver of domestic economic growth as well as of the country’s foreign policy.
3. Bent on nuclear domination: Continuing the policies of President Obama, the Trump administration envisions a massive modernization of America’s nuclear arsenal, to the tune of at least a trillion dollars over the next generation. Much like an old-guard Soviet premier, Trump has boasted that America will always remain at “the top of the pack” when it comes to nuclear weapons.
4. Imperialist and expansionist: Historians speak of America’s “informal” empire, by which they mean the U.S. is less hands-on than past imperial powers like the Romans and the British. But there’s nothing informal or hands-off about America’s 800 overseas military bases or the fact that its Special Operations forces are being deployed in 130 or more countries yearly. When the U.S. military speaks of global reach, global power, and full-spectrum dominance, this is traditional imperialism cloaked in banal catchphrases. Put differently, Soviet imperialism, which American leaders always professed to fear, never had a reach of this sort.
5. Persecutes critics and dissidents: Whether it’s been the use of the Patriot Act under George W. Bush’s presidency, the persecution of whistleblowers using the World War I-era Espionage Act under the Obama administration, or the vilification of the media by the new Trump administration, the U.S. is far less tolerant of dissent today than it was prior to the Soviet collapse. As Homeland Security Secretary and retired four-star Marine General John Kelly recently put it, speaking of news stories about the Trump administration based on anonymous intelligence sources, such leaks are “darn close to treason.” Add to such an atmosphere Trump’s attacks on the media as the “enemy” of the people and on critical news stories as “fake” and you have an environment ripe for the future suppression of dissent.
In the Soviet Union, political opponents were often threatened with jail or worse, and those threats were regularly enforced by men wearing military or secret police uniforms. In that context, let’s not forget the “Lock her up!” chants led by retired Lt. General Michael Flynn at the Republican National Convention and aimed at Donald Trump’s political opponent of that moment, Hillary Clinton.
6. Internal problems like drug abuse, inadequate health care, and a poisoned environment: Alcoholism is still rife in Russia and environmental damage widespread, but consider the U.S. today. An opioid crisis is killing more than 30,000 people a year. Lead poisoning in places like Flint, Michigan, and New Orleans is causing irreparable harm to the young. The disposal of wastewater from fracking operations is generating earthquakes in Ohio and Oklahoma. Even as environmental hazards proliferate, the Trump administration is gutting the Environmental Protection Agency. As health crises grow more serious, the Trump administration, abetted by a Republican-led Congress, is attempting to cut health-care coverage and benefits, as well as the funding that might protect Americans from deadly pathogens. Disturbingly, as with the Soviet Union in the era of its collapse, life expectancy among white men is declining, mainly due to drug abuse, suicide, and other despair-driven problems.
7. Extensive prison systems: As a percentage of its population, no country imprisons more of its own people than the United States. While more than two million of their fellow citizens languish in prisons, Americans continue to see their nation as a beacon of freedom, ignoring Guantánamo Bay, Cuba. In addition, the country now has a president who believes in torture, who has called for the murder of terrorists’ families, and who wants to refill Guantánamo with prisoners. It also has an attorney general who wants to make prison terms for low-level drug offenders ever more draconian.
8. Stalemated wars: You have to hand it to the Soviets. They did at least exhibit a learning curve in their disastrous war in Afghanistan and so the Red Army finally left that country in 1989 after a decade of high casualties and frustration (even if its troops returned to a land on the verge of implosion). U.S. forces, on the other hand, have been in Afghanistan for 16 years, with the Taliban growing ever stronger, yet its military’s response has once again been to call for investing more money and sending in more troops to reverse the “stalemate” there. Meanwhile, after 14 years, Iraq War 3.0 festers, bringing devastation to places like Mosul, even as its destabilizing results continue to manifest themselves in Syria and indeed throughout the greater Middle East. Despite or rather because of these disastrous results, U.S. leaders continue to over-deploy U.S. Special Operations forces, contributing to exhaustion and higher suicide rates in the ranks.
In light of these eight points, that lighthearted Beatles tune and relic of the Cold War, “Back in the USSR,” takes on a new, and far harsher, meaning.
What Is to Be Done?
Slowly, seemingly inexorably, the U.S. is becoming more like the former Soviet Union. Just to begin the list of similarities: too many resources are being devoted to the military and the national security state; too many over-decorated generals are being given too much authority in government; bleeding-ulcer wars continue unstanched in Afghanistan, Iraq, and elsewhere; infrastructure (roads, bridges, pipelines, dams, and so on) continues to crumble; restless “republics” grumble about separating from the union (Calexit!); rampant drug abuse and declining life expectancy are now American facts of life. Meanwhile, the latest U.S. president is, in temperament, authoritarian, even as government “services” take on an increasingly nepotistic flavor at the top.
I’m worried, comrade! Echoing the cry of the great Lenin, what is to be done? Given the list of symptoms, here’s one obvious 10-step approach to the de-sovietization of America:
1. Decrease “defense” spending by 10% annually for the next five years. In the Soviet spirit, think of it as a five-year plan to restore our revolution (as in the American Revolution), which was, after all, directed against imperial policies exercised by a “bigly” king.
2. Cut the number of generals and admirals in the military by half, and get rid of all the meaningless ribbons, badges, and medals they wear. In other words, don’t just cut down on the high command but on their tendency to look (and increasingly to act) like Soviet generals of old. And don’t allow them to serve in high governmental positions until they’ve been retired for at least 10 years.
3. Get our military out of Afghanistan, Iraq, and other war-torn countries in the Greater Middle East and Africa. Reduce that imperial footprint overseas by closing costly military bases.
4. Work to eliminate nuclear weapons globally by, as a first step, cutting the vast U.S. arsenal in half and forgetting about that trillion-dollar “modernization” program. Eliminate land-based ICBMs first; they are no longer needed for any meaningful deterrent purposes.
5. Take the money saved on “modernizing” nukes and invest it in updating America’s infrastructure.
6. Curtail state surveillance. Freedom needs privacy to flourish. As a nation, we need to remember that security is not the bedrock of democracy — the U.S. Constitution is.
7. Work to curb drug abuse by cutting back on criminalization. Leave the war mentality behind, including the “war on drugs,” and focus instead on providing better treatment programs for addicts. Set a goal of cutting America’s prison population in half over the next decade.
8. Life expectancy will increase with better health care. Provide health care coverage for all using a single-payer system. Every American should have the same coverage as a member of Congress. People shouldn’t be suffering and dying because they can’t afford to see a doctor or pay for their prescriptions.
9. Nothing is more fundamental to “national security” than clean air and water. It’s folly to risk poisoning the environment in the name of either economic productivity or building up the military. If you doubt this, ask citizens of Russia and the former Soviet Republics, who still struggle with the fallout from the poisonous environmental policies of Soviet days.
10. Congress needs to assert its constitutional authority over war and the budget, and begin to act like the “check and balance” it’s supposed to be when it comes to executive power.
There you have it. These 10 steps should go some way toward solving America’s real Russian problem — the Soviet one. Won’t you join me, comrade?
William J. Astore, a retired lieutenant colonel (USAF) and history professor, is a TomDispatch regular. His personal blog is Bracing Views.